What Is Proof of Knowledge?
A proof of knowledge is a cryptographic proof in which a “prover” convinces a “verifier” that it knows some information.
Cryptographic proofs are seeing a Cambrian explosion of innovation in Web3. Many of these advancements have to do with zero-knowledge proofs—a subset of knowledge proofs, or proofs of knowledge.
<div class="educational-divider sections-divider"></div>
Proof of Knowledge Explained
In a proof of knowledge, a prover must prove that it knows something to a verifier. Exactly what is being proved varies between proof protocols.
The terms “prover” and “verifier” are commonly used to describe cryptographic proofs. The prover is the entity or program that creates the cryptographic proof. The verifier is the entity or program that checks the proof’s contents.
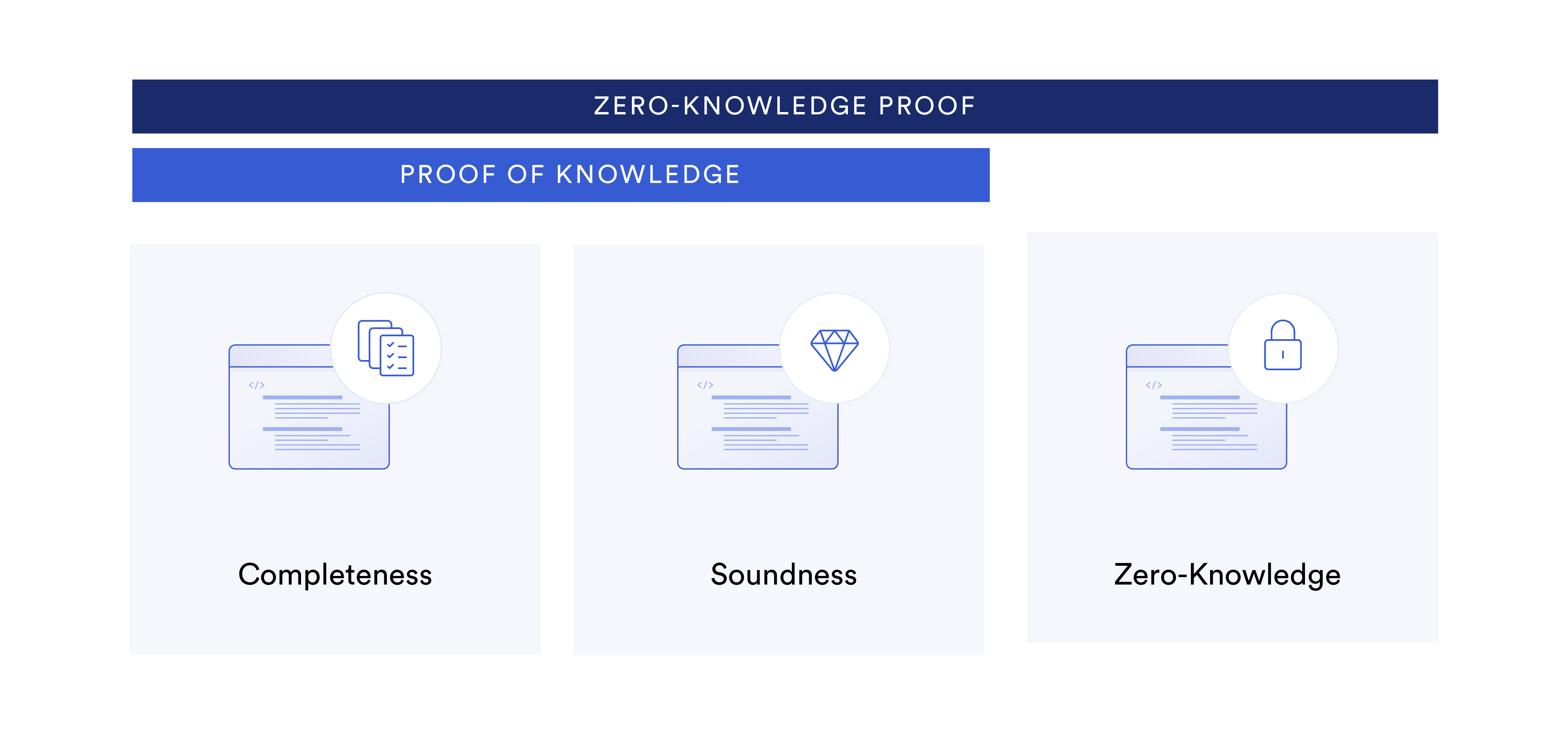
A proof of knowledge has two fundamental characteristics:
- Completeness: If a statement is true, then an honest verifier can be convinced by an honest prover that they possess knowledge about the correct input.
- Soundness: If a statement is false, then no dishonest prover can unilaterally convince an honest verifier that they possess knowledge about the correct input.
The key difference between a proof of knowledge and a zero-knowledge proof is that a zero-knowledge proof has an additional characteristic:
- Zero-knowledge: If a statement is true, then the verifier learns nothing more from the prover other than that the statement is true.
Another way to classify proofs of knowledge, including zero-knowledge proofs, is by interactivity—knowledge proofs are either interactive or non-interactive. Interactive zero-knowledge proofs require direct communication in rounds between the prover and the verifier, while non-interactive zero-knowledge proofs can be verified without any direct interaction between the two parties.
Note: Non-interactive variations of knowledge proofs that are not zero knowledge are sometimes called signature schemes.
<div class="educational-divider sections-divider"></div>
Applications of Proof of Knowledge
Proofs of knowledge have a wide variety of applications for advancing digital identity, security, and privacy within blockchain networks and beyond.
Zero-Knowledge Cloud Storage and Password Management
Cloud storage and password management providers that offer zero-knowledge encryption use zero-knowledge proofs to verify whether a user has knowledge of an encryption key (which affords access to stored files or passwords) without needing to store the encryption key on their servers.
Schnorr Signatures in Bitcoin
Schnorr signatures, which use a non-interactive proof of knowledge (signature scheme), were implemented within the Bitcoin protocol during the Taproot upgrade. They enable the aggregation of multiple digital signatures into a single signature while still enabling a verifier to definitively know that all individual entities behind the aggregated signature have signed the transaction.
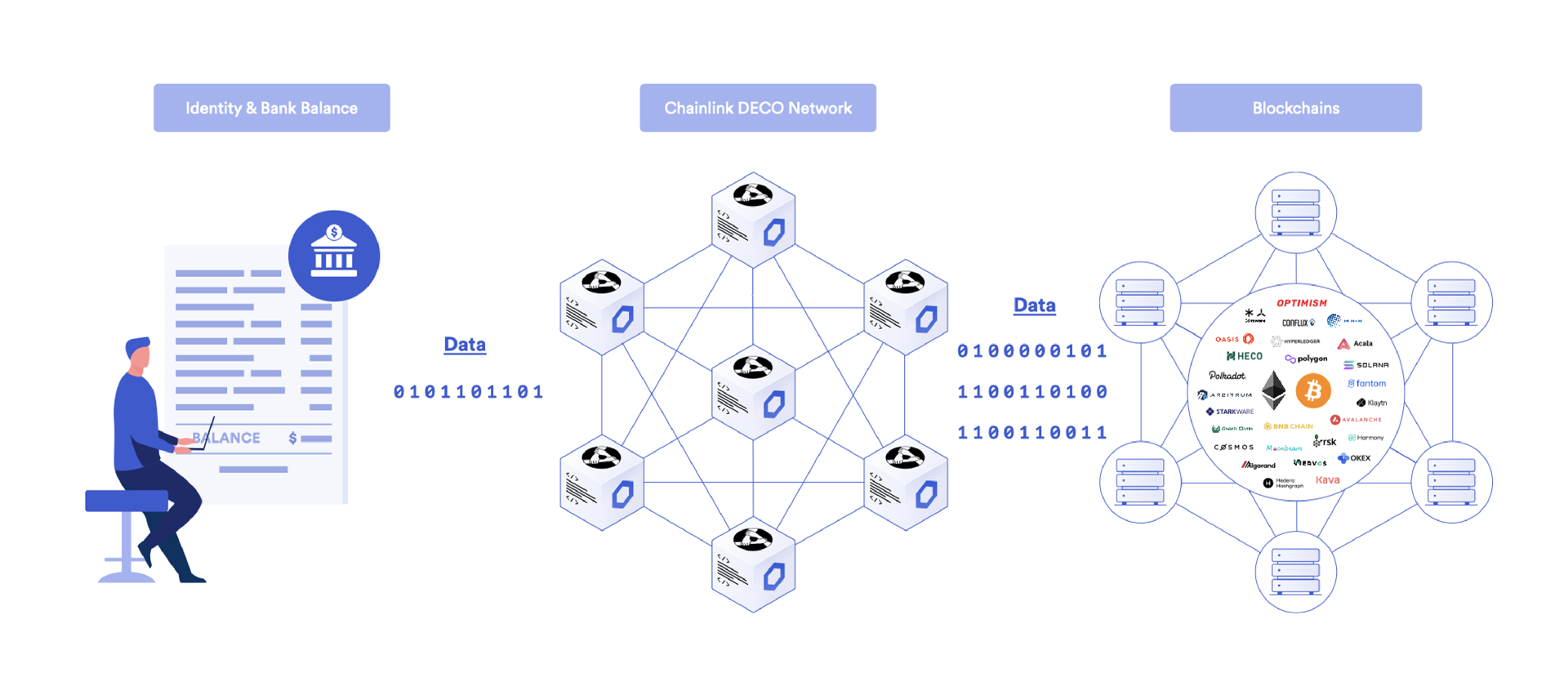
Privacy-Preserving Digital Identity Using DECO
Chainlink DECO is a privacy-preserving oracle service currently in development that uses zero-knowledge proofs to prove specific statements regarding a user—such as their bank account balance or health data—without revealing any specifics of the underlying information.
<div class="educational-divider sections-divider"></div>
Conclusion
While proofs of knowledge come in a wide range of formats and flavors, the core premise of all knowledge proof protocols is that they provide more security, privacy, and usability within Internet-based technologies.