Market Manipulation vs. Oracle Exploits
An oracle exploit is when an oracle reports inaccurate data about an external event, usually as a result of nefarious influence.
Secure blockchain oracles are at the heart of Web3, enabling a diverse range of decentralized applications that reduce counterparty risk and enable the frictionless exchange of value. When it comes to price feeds that help DeFi applications by providing access to financial market data, developers must not only ensure that the oracles they integrate are secure from tampering and properly incentivized, but also consider the quality and manipulation resistance of the underlying markets that the oracles are configured to track.
In this blog, we explore the differences between market manipulation and oracle exploits, how Chainlink Price Feeds are designed to report the market-wide price of assets, and ways for developers to increase the security of their applications.
What Is Market Manipulation?
Market manipulation is when the price of an asset is artificially manipulated through the alteration of natural supply and demand forces. It’s a deliberate action undertaken by a malicious actor, usually with the intention of making a profit at the expense of other traders.
Low-Liquidity Assets Are More Vulnerable to Manipulation
The ability of a malicious actor to manipulate prices depends on the liquidity of an asset. Liquidity refers to how easy it is to buy or sell an asset without impacting its price. The greater an asset’s liquidity, the more capital it takes to manipulate its price. Conversely, the lower the liquidity, the less expensive it can be. This is why thinly traded assets with low liquidity are more vulnerable to market manipulation and can present risk when used within financial products.
The liquidity of an asset depends on its trading volume, market depth, and trading markets. Here’s the definition of each and why they matter:
- Trading volume—Trading volume is the amount an asset was traded during a specific period. High trading volume is an indicator of a highly liquid market. However, assets can have high trading volume while lacking market depth.
- Market depth—Market depth refers to the number of standing buy and sell bids at various price levels. It indicates the ability of a market to absorb unusually large orders without correspondingly large price swings.
- Trading markets—Assets trade on various platforms simultaneously, including centralized exchanges, decentralized exchanges (DEXs), and OTC (over-the-counter) desks. The liquidity on an individual platform may be lower than the market as a whole, especially when there’s insufficient volume to incentivize the arbitrage traders that help create cross-platform markets. This means that even if a specific asset may be highly liquid in the market as a whole, it could have low liquidity on specific exchanges.
Market Manipulation Methods To Protect Against
As a general term, market manipulation can encapsulate a wide variety of techniques. Examples of market manipulation techniques used across both traditional finance and DeFi include but are not limited to:
- Spoofing—Posting trade orders without the intention of executing them. A bot may be used to post a large number of orders that impact the behavior of buyers and sellers and then cancel those orders before they go through.
- Ramping—Trades that artificially increase the market price of an asset to drive demand from actual buyers, who the malicious actor then sells to.
- Bear raid—Attempts to artificially lower the market price of an asset through heavy selling or short selling.
- Cross-market manipulation—Making trades in a trade environment to manipulate the price in another environment in order to make additional trades that profit from the divergence in price.
- Wash trading—Both buying and selling an asset to give the impression of a higher trade volume in order to attract legitimate traders to the market.
- Frontrunning—Making trades based on insider information that the rest of the market doesn’t have access to or before it can respond. In crypto, frontrunning is part of MEV.
These tactics can target either a subset of an asset’s trading environment or the market-wide price. Targeting a smaller sector of an overall market can be less costly to a malicious actor, although these attacks can be easier to defend against and the opportunity to extract funds can be smaller than manipulating the market-wide price.
Risks of Market Manipulation for DeFi Protocols
Over the past couple of years, market manipulation has resulted in a notable amount of aggregate value being exploited across DeFi in various ways. While the price oracle used by a DeFi protocol to receive financial market data may be operating without issue, protocols can still be at risk if the underlying markets on which the oracle reports are manipulated.
DeFi platforms potentially at risk of market manipulation include:
- Money markets—Lending protocols can accrue toxic debt and even become insolvent if they don’t liquidate undercollateralized positions in a timely and efficient manner. Users’ funds can also be unfairly liquidated based on artificial price changes, resulting in losses.
- Options markets—Similar to money markets, options markets must trigger liquidations efficiently to stay solvent. These liquidations can be unwarranted.
- Synthetic assets—Liquidity providers can lose their assets if positions based on artificial prices are paid out or used to create bad loans.
- Algorithmic stablecoins—Stablecoins can lose their peg if the stabilization mechanism and implicit incentives are broken due to artificial price movements.
- Automated asset management—Trading algorithms that respond to artificial prices can make trades that lead to poor investment outcomes.
What Is an Oracle Exploit?
Oracles deliver external data such as digital asset prices, the outcomes of sports matches, and weather information to blockchains and smart contracts.
An oracle exploit occurs when an oracle reports inaccurate data about an event or state of the external world. This can happen because the oracle purposefully acts maliciously or negligently, or the oracle’s data source is compromised.
Oracle Exploit Due to Misreporting
Misreporting is when an oracle reports a price that differs from the correct market-wide price of an asset. Regardless of whether misreporting occurs due to malicious or negligent behavior, any protocol relying on a faulty oracle for price data may be at risk of an exploit.
For example, if the actual market-wide price of an asset is $100 but the oracle misreports an arbitrary value of $50, this could lead to exploits on a lending platform that uses the oracle’s price data to trigger liquidations. Even though the liquidation engine functions as designed, it unfairly liquidates user assets because of the misreported asset price.
Oracle Exploit as a Result of Poor Market Coverage
Poor market coverage can lead to oracles misreporting the price of an asset. Relying on only a subset of all trading environments makes them vulnerable to an oracle exploit if that subset is manipulated, even when the majority of trading environments and the market-wide price remain unaffected.
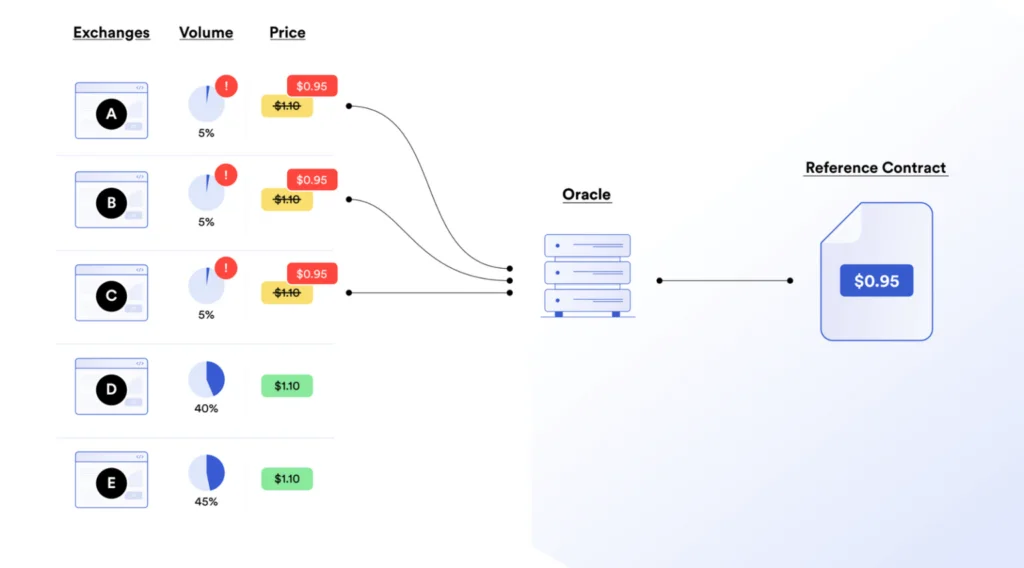
For example, if an asset is traded across five exchanges and 85% of trading volume takes place on two of those exchanges, relying on the other three low-liquidity exchanges for price inputs would give the oracle poor market coverage. If a malicious actor manipulated the price on those three low-liquidity exchanges, then the oracle would report a price that differs from the actual market-wide price, leading to possible exploits.
Highly Secure Oracles
The risk of oracle exploits can be mitigated with more secure oracle design. Features of secure oracles include sourcing price data from across all trading environments to provide proper market-wide coverage, protections from external tampering that eliminate single points of failure via decentralization, and economic incentives to report faithfully that align oracles with their users.
An oracle without these defensive measures and aligned incentives is vulnerable to misreporting an asset’s price, while highly secure oracles mitigate manipulation attempts and accurately report the actual market-wide price.

Risks of Oracle Exploits for DeFi Protocols
The negative consequences of oracle exploits for DeFi protocols—such as money markets, options markets, synthetic assets, algorithmic stablecoins, and automated asset management—include depegged stablecoins, malicious arbitrage trades, unwarranted liquidations, and protocol insolvency. While the risks of oracle exploits are similar to the risks of market manipulation, they stem from a different root cause.
This is because both market manipulation and oracle exploit attacks leverage artificial changes in price data that diverge from the natural supply and demand forces of the market. So while the risks may be similar, the mechanisms that make them possible differ.
What Is the Fundamental Difference Between Market Manipulation and Oracle Attacks?
Market manipulation changes the price of an asset, while oracle attacks result in incorrect or invalid data being reported that doesn’t reflect true asset pricing. Because the end result is an asset price that leads to a loss of funds, these issues have historically been confused and conflated.
Altering the underlying supply and demand dynamics of an asset to the extent that its price is affected is the basis for market-based price attacks. Properly designed oracles accurately report prices based on the actual market-wide price of an asset, regardless of the level of healthy liquidity in the asset’s underlying markets. If the market-wide price of an asset has been manipulated, the oracle will still report that price—it’s what oracles are designed to do.
What’s different about oracle attacks is that the market price can still be based on real supply and demand pressure. Instead, the oracle reports false information through either unintentional or malicious behavior.
Example Highlighting the Point of Failure
As the above table highlights, the point of failure for market manipulation and oracle attacks is different. Imagine an asset that, based on natural supply and demand forces, would be trading at $100. In the market manipulation example, the natural market price of $100 has been artificially increased to $200; this is the point of failure—the oracle is accurately reporting the $200 market price. In contrast, the oracle attack example shows that the overall market price remains unchanged at $100. The oracle misreporting the price as $70 is the point of failure.
To build a secure DeFi protocol that protects users from market manipulation and oracle attacks, developers must consider the security properties of both the oracle they use as well as the quality of an asset’s underlying market, including its market volume, depth, and trading environments. If these considerations are not taken into account, then a protocol may be designed in a way that does not properly mitigate risk.
Chainlink Price Feeds Protect dApps From Oracle Exploits
In order to mitigate the risk of oracle exploits, applications can integrate Chainlink Price Feeds to access high-quality, tamper-proof market data.
Chainlink Price Feeds have a range of security features, including:
- Multiple layers of decentralization—Decentralized architecture at the data source, node operator, and oracle network levels mitigates single points of failure and helps ensure each oracle report reflects the true market-wide price of assets.
- Hyper-reliable oracle node operators—Geographically distributed collections of Sybil-resistant, security-reviewed, and highly experienced node operators are responsible for delivering price data to Web3 networks.
- Defense-in-depth approach—On-chain transparency, active monitoring, failover capabilities and disaster recovery, backup oracle networks, and more underpin a multi-layered design.
Chainlink Price Feeds in the Presence of Market Manipulation
If the market-wide price of an asset is manipulated, Price Feeds will report that price because it accurately reflects the current state of the market—the accurate truth. But if only a small subset of an asset’s underlying market is manipulated (e.g. a few low-liquidity markets), then Chainlink Price Feeds are designed to still report the accurate overall market-wide price, helping protect from such manipulation attempts.
Along with Chainlink Price Feeds’ multiple layers of aggregation, the use of volume-weighted average price (VWAP) methodology (plus similar methodologies) and outlier detection plays a key role in preventing market manipulation within subsections of the overall market from influencing reported asset prices. VWAP mechanisms place more emphasis on where more trading activity takes place and seamlessly adapt as liquidity moves across various markets, while data aggregators commonly filter out market anomalies like flash crashes, wash trading, and other outliers so they don’t influence the final aggregated data point.
Explore Chainlink Price Feeds
How DeFi Developers Can Protect Their dApps
The first step for DeFi developers who need to protect their dApps is to integrate Chainlink Price Feeds for highly accurate, tamper-proof, and hyper-reliable price data. Next, developers must consider the quality of the assets their protocol supports.
Thinly traded assets can make protocols vulnerable to exploits when used as collateral, as they’re easier for malicious actors to manipulate. Therefore, detailed market risk analysis should be performed to provide insight into what the loan-to-value ratio of loans should be to help ensure solvency and mitigate risk exposure.
Consider further layers of security in your dApp:
- Circuit breakers—In the case of an extreme price event, the contract would pause operations for a limited period of time.
- Contract update delays—Contracts would not update until the protocol had received a recent fresh input from the data feed.
- Manual kill switch—If a vulnerability or bug is discovered in one of the upstream contracts, the user can manually cease operation and temporarily sever the connection to the data feed.
- Monitoring—Some users create their own monitoring alerts based on deviations in the data feeds that they are using.
Risk mitigation is not something to set and forget; it’s a continuous process of monitoring, updating, and refining processes based on evolving market conditions. For more information, please refer to the Chainlink documentation which outlines developer responsibilities and risk mitigation precautions.
Highly Secure dApps Unlock DeFi Mass Adoption
For non-crypto-native users to adopt DeFi applications in their everyday lives, the security guarantees must be unparalleled. Mitigating market manipulation and oracle exploits is a must. While Chainlink helps protect against oracle exploits, developers must also implement safeguards, and users should always do their own research before depositing assets to an application. Ultimately, securing assets across Web3 requires a multifaceted approach, and we must all work together to ensure users’ funds remain safe and secure.
If you are a DeFi developer and want to integrate Chainlink Price Feeds, check out our documentation, ask a question in Discord, or set up a call with an expert.